I was addressing an interesting issue for a customer today where a user with a shared mailbox would not automatically update. Their primary mailbox updated correctly, only the shared mailbox did not update.
All other shared mailboxes for other users worked correctly.
All users are running Outlook 2013 32bit with all latest patches at the time of this writing.
When a user navigates to the shared mailbox and clicks Send/Receive All Folders or Update Folder, it will not update.
The only way the user can update the shared mailbox is by closing and reopening Microsoft Outlook.
All other users in the environment do not have issues with shared mailboxes.
After doing some research, it appears to be an issue with Microsoft Outlook when dealing with shared mailboxes over 2GB in size. This shared mailbox having the issue was indeed over 2GB in size.
There are numerous forum threads on the Internet with people experiencing this Outlook issue:
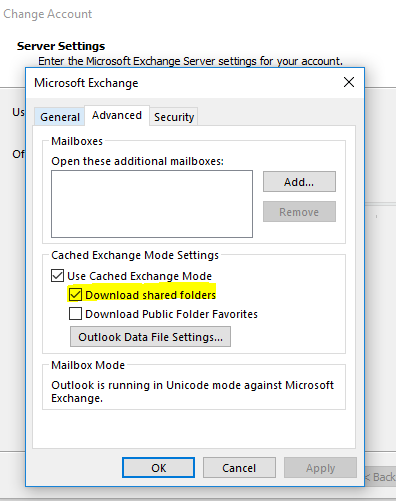
As a workaround, simply prevent the shared mailboxes from being cached locally by disabling "Download shared folders" on the users Outlook profile. This is a confirmed workaround to the issue.
All other shared mailboxes for other users worked correctly.
All users are running Outlook 2013 32bit with all latest patches at the time of this writing.
When a user navigates to the shared mailbox and clicks Send/Receive All Folders or Update Folder, it will not update.
The only way the user can update the shared mailbox is by closing and reopening Microsoft Outlook.
All other users in the environment do not have issues with shared mailboxes.
After doing some research, it appears to be an issue with Microsoft Outlook when dealing with shared mailboxes over 2GB in size. This shared mailbox having the issue was indeed over 2GB in size.
There are numerous forum threads on the Internet with people experiencing this Outlook issue:
- https://community.spiceworks.com/topic/534218-office-365-shared-mailbox-not-updating-for-one-user-only
- https://social.technet.microsoft.com/Forums/exchange/en-US/b2edd2f5-15c6-405a-b2fd-c365d4fa7e6f/outlook-2010-shared-mailbox-in-cache-mode-not-updating-inbox-automatically?forum=exchange2010
- https://www.reddit.com/r/msp/comments/4qc7z0/office_365_shared_mailboxes_not_updating/
As a workaround, simply prevent the shared mailboxes from being cached locally by disabling "Download shared folders" on the users Outlook profile. This is a confirmed workaround to the issue.